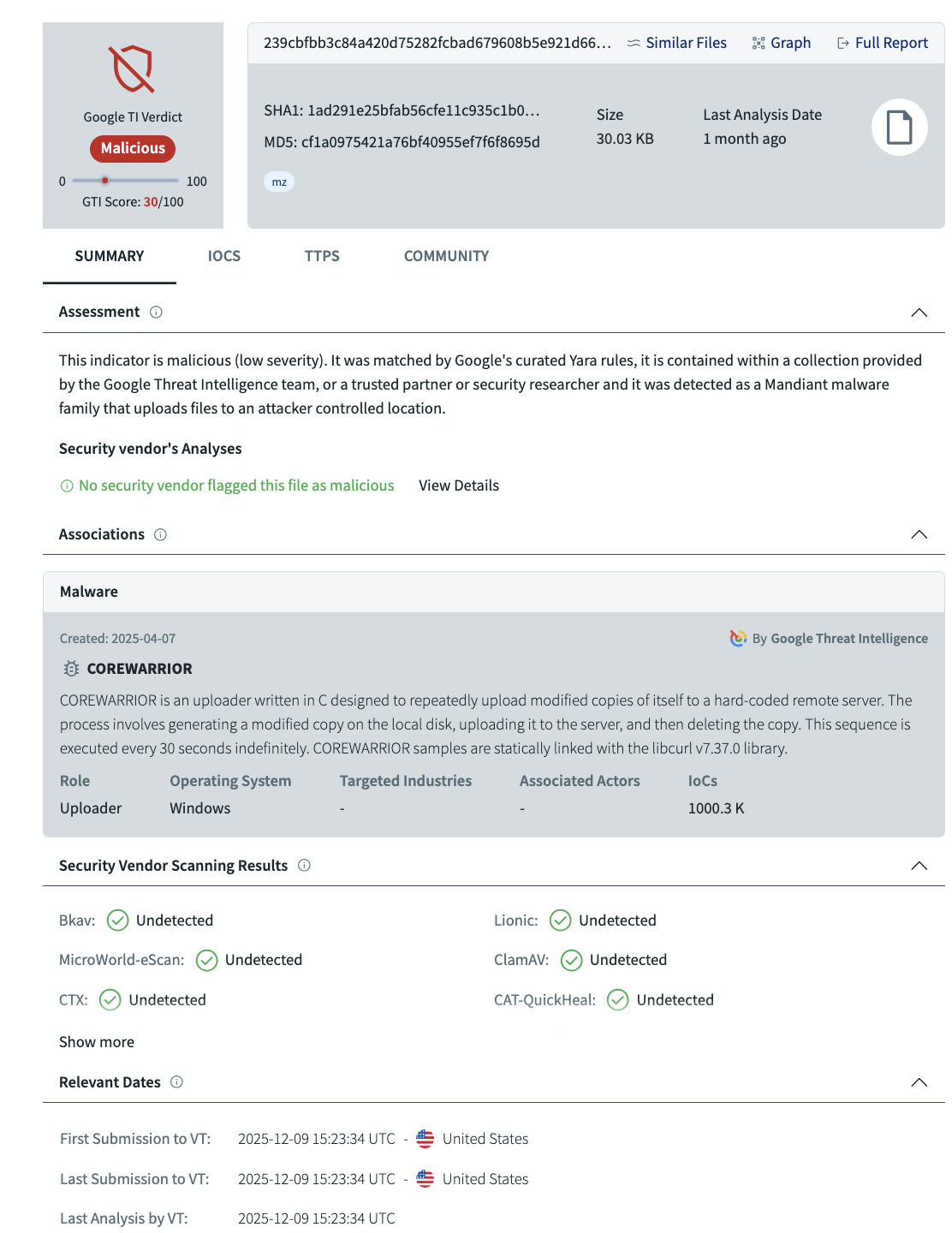
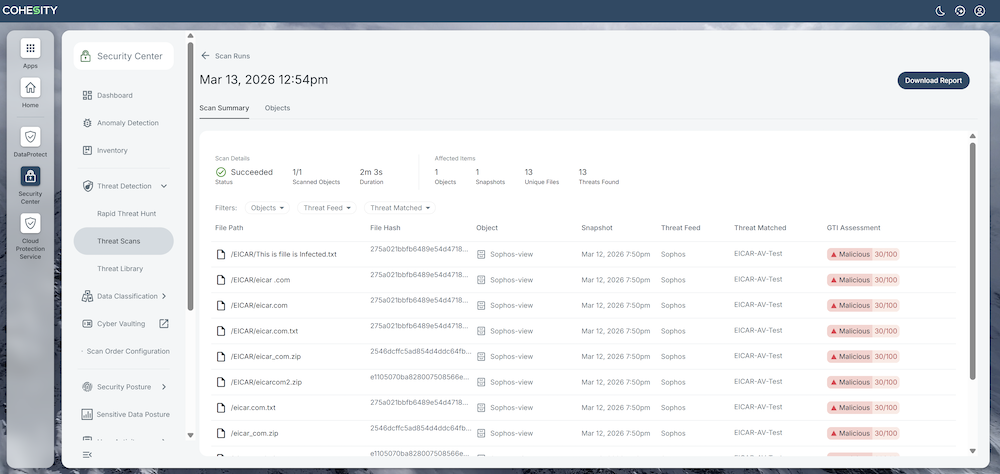
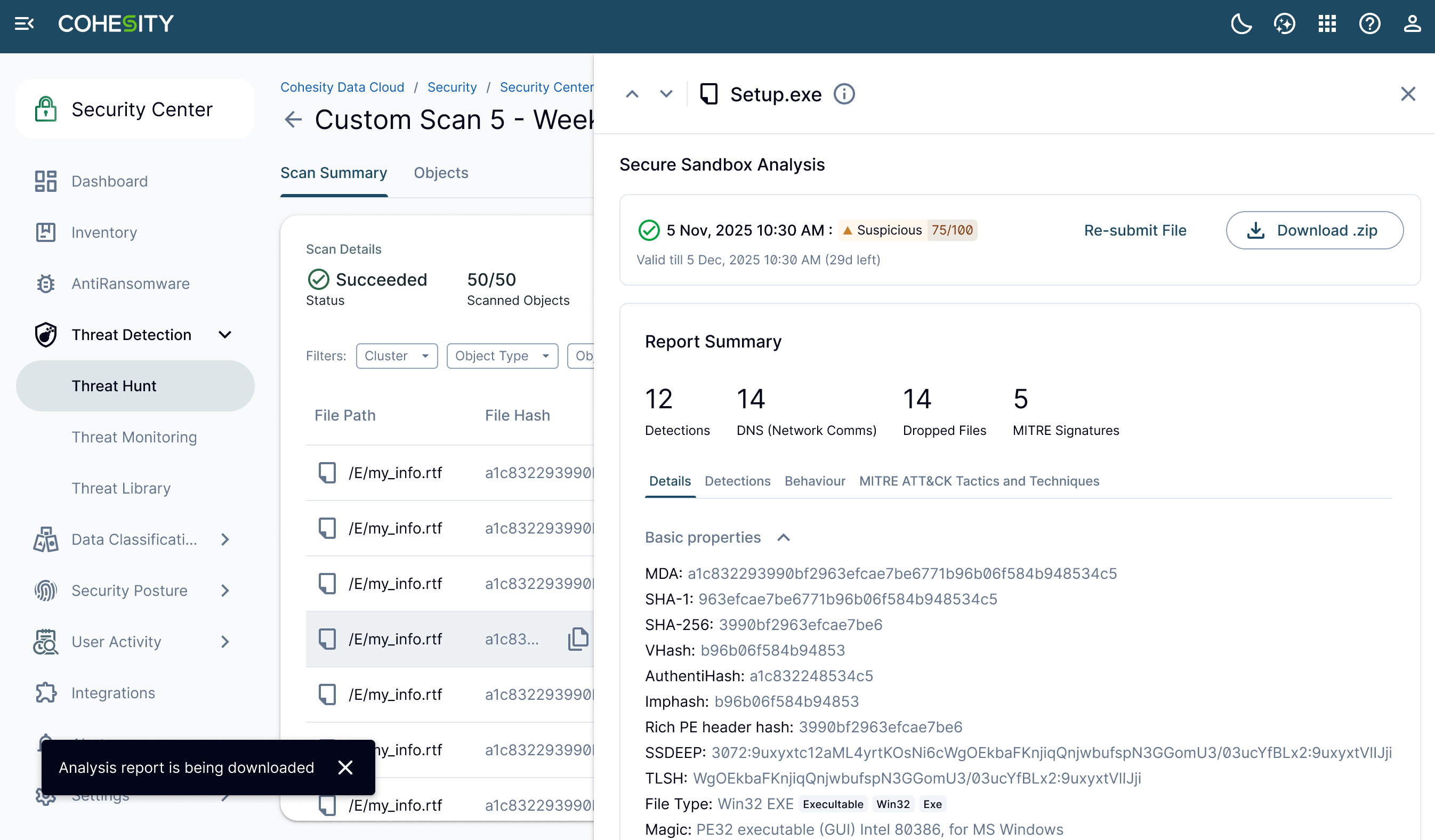
Threat protection refers to the strategies, tools, and technologies used to defend against malicious software, or malware. Malware includes a wide range of harmful software such as viruses, worms, Trojans, ransomware, spyware, and adware, among others.
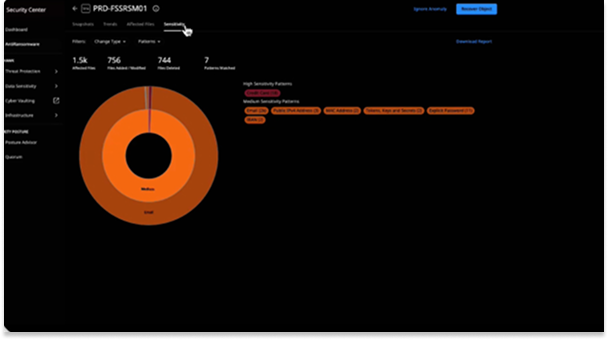
Effective threat protection involves creating an integrated security architecture with several layers of defense, including antivirus software, firewalls, email and web filtering, and patch management. Combined with user education and training, organizations can significantly reduce their risk of falling victim to malware attacks and protect their sensitive data and systems from compromise.