Defending Microsoft Entra ID: How to Stop Cloud Identity Attacks
Overview
Recent incidents, including the Stryker breach, have demonstrated a devastating reality: attackers gaining access to a single privileged Microsoft Entra ID administrator account can trigger catastrophic, immediate damage across an entire global enterprise - without deploying a single line of malware. In the most severe cases, attackers create a shadow Global Administrator account and leverage Microsoft's own Intune remote management platform to issue factory-reset commands to every enrolled device in the tenant within hours of initial access.
These attacks represent a crystallizing moment for enterprise identity security. Entra ID - Microsoft's cloud identity and access management platform, serving over 600 million users across roughly 300,000 organizations - has become what on-premises Active Directory once was: the single plane of glass through which an organization's entire digital estate can be controlled. Compromise it, and you own everything attached to it.

The Entra ID Kill Chain
Unlike traditional ransomware kill chains that involve payload delivery, persistence, and lateral movement across endpoints, the Entra ID kill chain operates entirely in the cloud identity plane. Each stage can be executed remotely, without touching a single endpoint, until the very last step.

The Five Attack Classes
Each stage of the kill chain is enabled by one or more distinct attack techniques. Understanding how each works is the prerequisite to detecting and blocking them.



MITRE ATT&CK for Cloud — TTP Mapping

Detection: KQL Queries for Microsoft Sentinel
The following queries target the highest-signal detection opportunities across the kill chain. Each can be deployed directly in Microsoft Sentinel or Defender.
1. AiTM IP Deviation:
Fires when the same identity authenticates successfully from more than one IP within a 10-minute window — the primary signal for token replay after AiTM capture.

2. Device Code Abuse:
Surfaces all device code flow authentications originating from unmanaged or non-compliant devices — the attacker scenario. Legitimate device code use (conference room devices, printers) will be from known, enrolled device IDs.

3. Rogue Admin Creation:
Zero-tolerance rule. Any new Global Admin assignment outside a known change window should be treated as an incident. Pair with PagerDuty or Slack webhook for immediate notification.

4. Bulk Intune Wipe:
This query is the last line of detection before impact. If Multi-Admin Approval is not configured, this alert is the only warning before devices are wiped. Lower the threshold to 1 for highly sensitive environments.

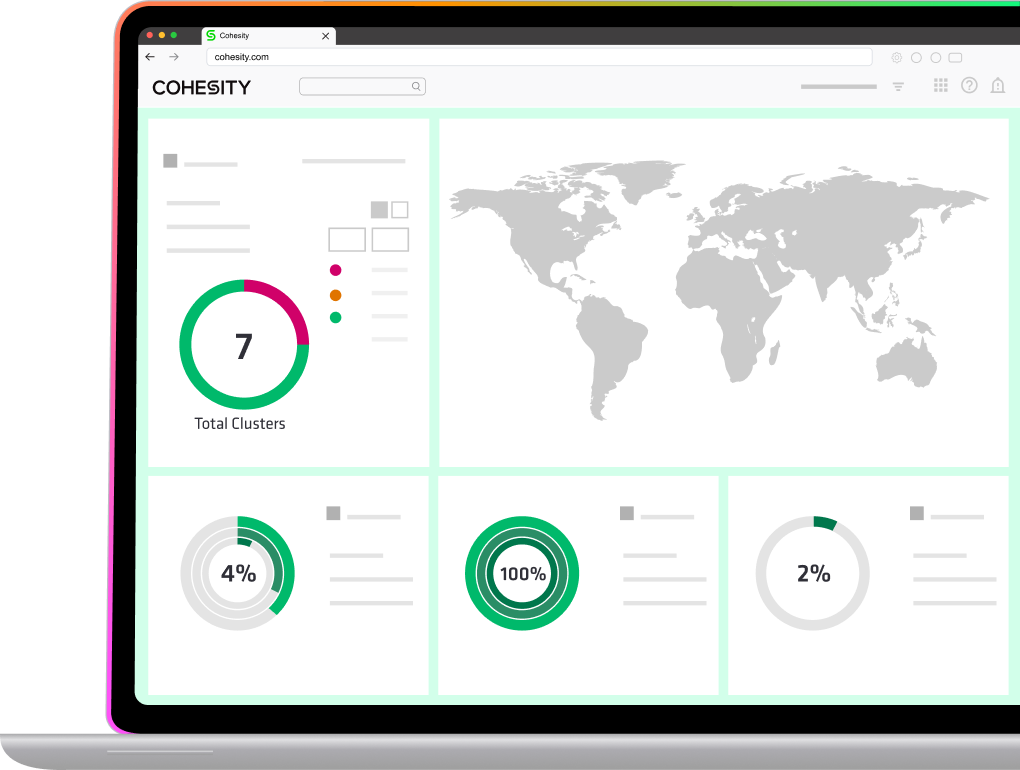
The Cohesity advantage

Identity resilience is the ability to secure, recover, and perform forensics on identity systems. This reduces the impact of a cyber event and decreases down time so an organization can bounce back quickly and securely. Identity systems like Active Directory and Entra ID are critical to the functioning of many organizations today. When they go down, business often grinds to a halt. At the same time, identity workloads can be very complex and challenging to protect and recover. It's critical to adopt the right solutions to make sure your critical identity infrastructure is protected end-to-end and you can recover them quickly and confidently.
How does Cohesity protect Active Directory and Entra ID from ransomware?
Cohesity has several solutions that help protect Active Directory and Entra ID across the entire attack lifecycle. First, we help to proactively harden your platforms by identifying vulnerabilities and excessive user privileges that can prevent a compromise or ransomware attack from occurring in the first place. If a ransomware attack has taken place, Cohesity can help you automate the process of recovery of your entire Active Directory forest in a few clicks and ensure that you can cleanly recover without internet access and with flexible OS provisioning. By protecting and recovering Active Directory first, you can restore the source of truth for Entra ID (since Entra ID is typically synced or federated to Active Directory). We also provide similar recovery solutions for Entra ID that allow you to recover with immutable, indelible, and durable backups.
How does Cohesity support identity recovery during cyber incidents?
Cohesity provides several solutions that automate the recovery process to up to a few clicks for Active Directory and Entra ID—cutting downtime by up to 90%. Cohesity also provides 24/7 expert incident response support and forensics to ensure that organizations recover from cyberattacks or catastrophic outages quickly and confidently.
Can I test or simulate identity recovery with Cohesity?
Yes, Cohesity Identity Resilience can help you test and simulate identity recoveries. Manual recoveries of Active Directory and Entra ID tend to be so difficult and complex that many organizations postpone or never test their identity recovery capabilities. Cohesity Identity Resilience makes it easy to test and simulate an identity recovery process.
Can Cohesity support protection and recovery of large AD environments?
Yes, Cohesity can support protection and recovery of both large AD environments with full Active Directory Forest recoveries in the case of a cyberattack and/or catastrophic outage. Cohesity can also support granular recoveries in the case of accidental deletions, misconfigurations, or restoring attributes.
How fast can I recover Active Directory and Entra ID after a cyberattack?
Cohesity enables customers to restore their critical identity infrastructure up to 90% faster with automated recoveries, speeding a typical recovery time of weeks to days or hours. Traditional recoveries of Active Directory and Entra ID can require over 40 manual steps that are complex and error-prone, adding more stress to the chaos of a cyber incident response.
Conclusion
In summary, Cohesity delivers a comprehensive approach to protecting and recovering identity infrastructure, ensuring organizations can rapidly respond to and recover from cyber incidents or outages. By automating recovery workflows, providing robust testing and simulation capabilities, and supporting both large-scale and granular recoveries, Cohesity empowers IT teams to minimize downtime and safeguard critical identity services like Active Directory and Entra ID. This proactive and resilient solution helps organizations maintain business continuity, build confidence in their security posture, and stay prepared for evolving threats.
For the latest advisories and technical details, visit Cohesity REDLab.

Ready to get started?
Start your 30-day free trial or view one of our demos.