Emerging Attack Patterns in the Wild
Cohesity REDLabs collects malicious files from multiple sources like CISA, Google Threat Intelligence, Ransomware.live and various open source projects. During the last 4 months, REDLab conducted analysis of MITRE TTPs associated with newly identified Indicators of Compromise (IoCs) in the wild. This threat intelligence report reveals critical shifts in adversary behavior, with December 2025 showing a dramatic escalation in automated collection, input capture, and process injection techniques.
MITRE Tactics, Techniques, and Procedures (TTPs) describe how adversaries behave during cyber attacks - what they aim to do and how they do it. Maintained by MITRE, an industry and government-backed non-profit organization, these behaviors are documented in the MITRE ATT&CK® framework (https://attack.mitre.org). TTPs are important because while tools and malware constantly change, attacker behaviors are more consistent, making TTPs a durable foundation for detection, threat hunting, and defense.
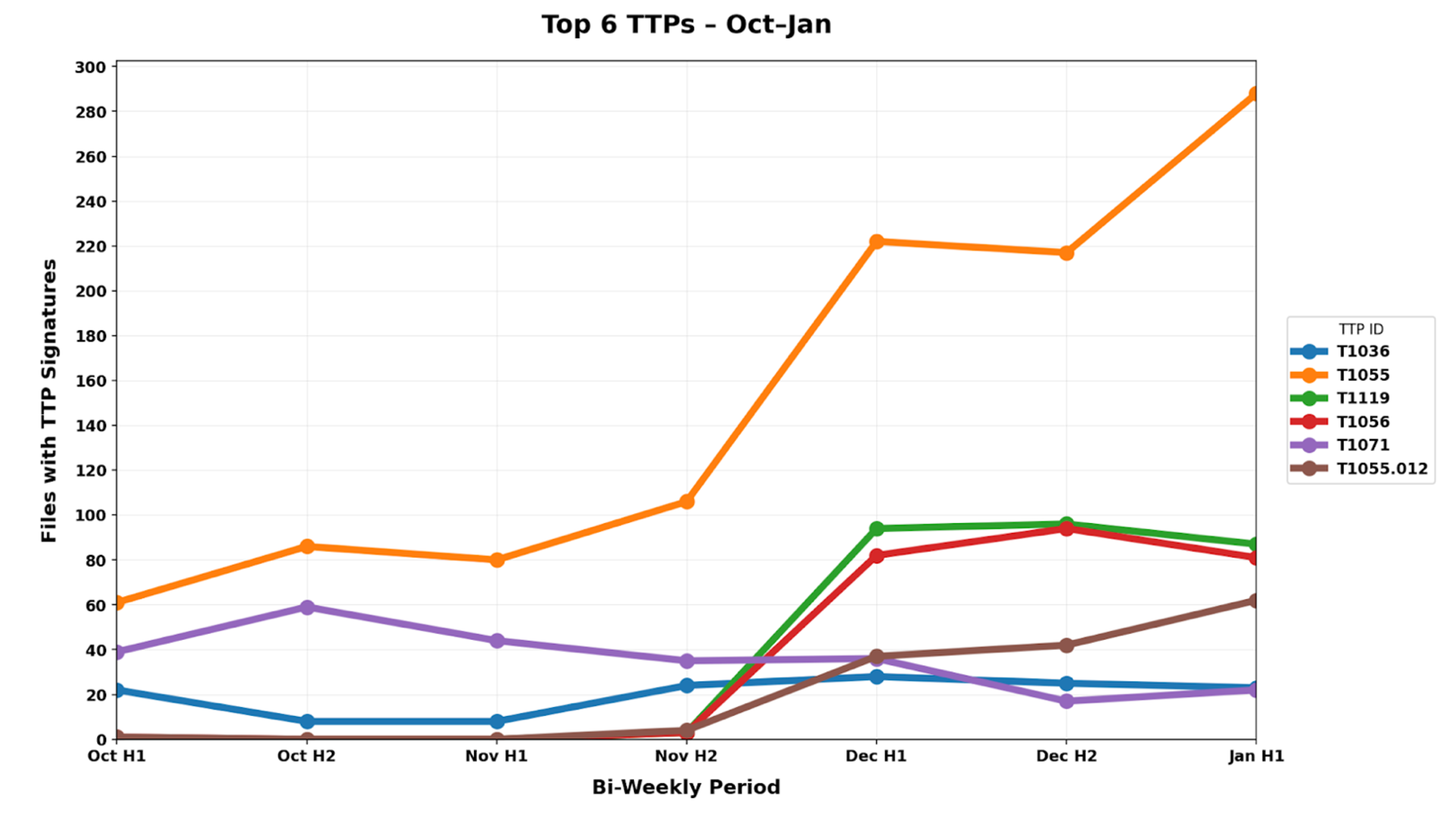
We identified persistent attack patterns that remained consistent throughout the quarter, as well as emerging techniques that appeared suddenly in December, signaling potential shifts in attacker toolkits and operational priorities.
Key Findings
- Persistent TTPs: The Unchanging Core of Modern Attacks
Our analysis reveals 3 TTPs that maintained consistent presence across all four months, representing the unchanging foundation of threat actor operations. These persistent techniques include T1055 (Process Injection) - enabling attackers to execute malicious code within legitimate processes to evade detection, T1071 (Application Layer Protocol) - facilitating command and control communications over standard protocols, and T1036 (Masquerading) - allowing malware to disguise itself as legitimate software. These techniques collectively account for over 72% of observed activity, with T1055 alone appearing in 58.55% of analyzed files. This consistency suggests these methods remain highly effective despite defensive awareness, as they leverage fundamental system functionalities that are difficult to restrict without impacting legitimate operations.
Percentage of files in which these top TTPs were observed in the period Oct’25 - Jan’26:
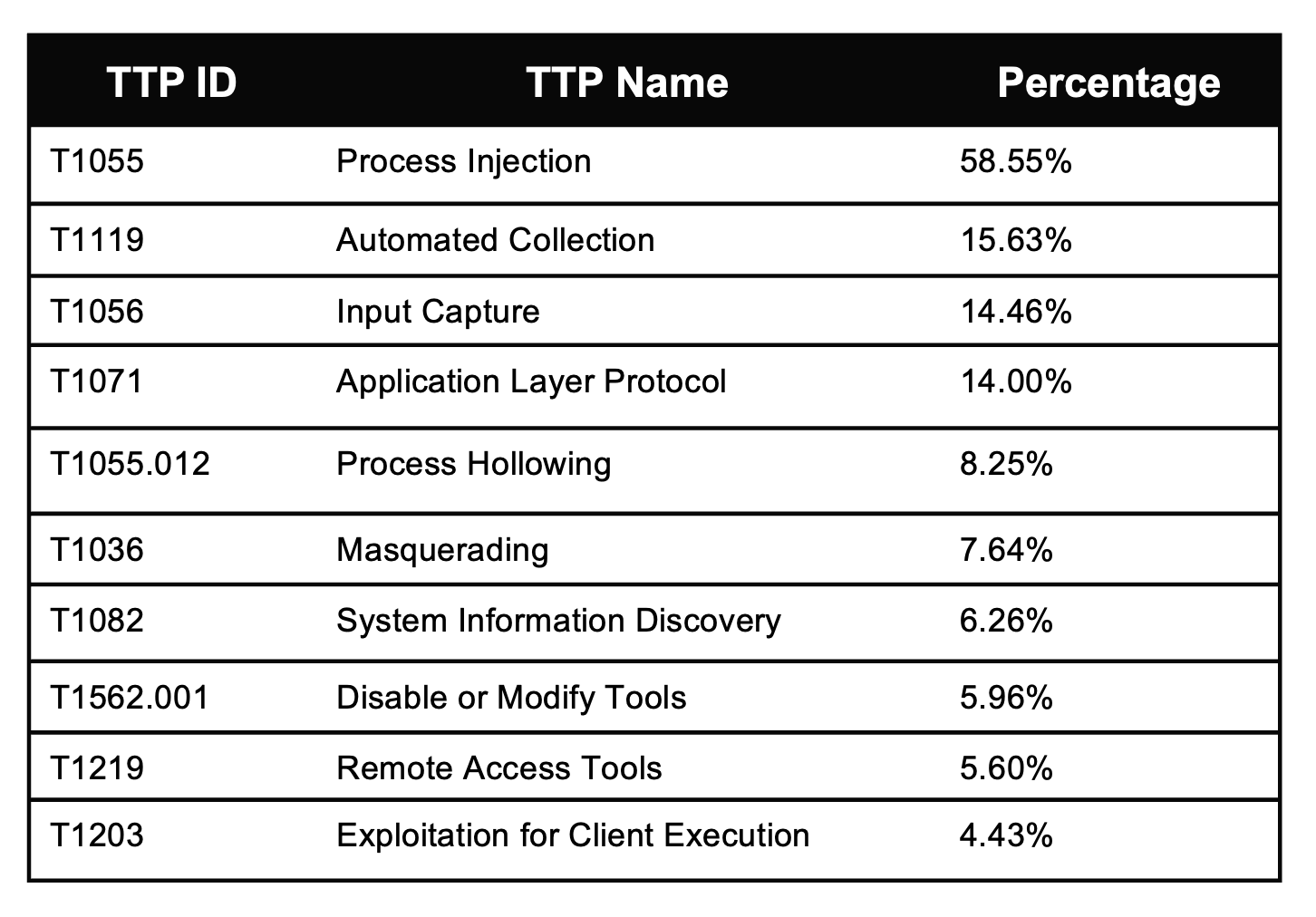
- Emerging Attack Patterns - December 2025 marked a notable shift in the threat landscape with 2 TTPs showing significant emergence compared to the October-November baseline. T1119 (Automated Collection) demonstrated a significant increase, rising from minimal presence in November to 25.64% in December, indicating a shift toward more systematic data theft operations. Additionally, T1056 (Input Capture) emerged as a prominent threat vector, appearing in 23.71% of December samples compared to negligible activity in previous months, suggesting increased focus on credential harvesting. T1055.012 (Process Hollowing), a specific process injection technique, also gained prominence at 10.82%. This evolution indicates adaptive threat actor behavior and potential preparation for Q1 2026 campaigns targeting sensitive credentials and automated data exfiltration.
Methodology
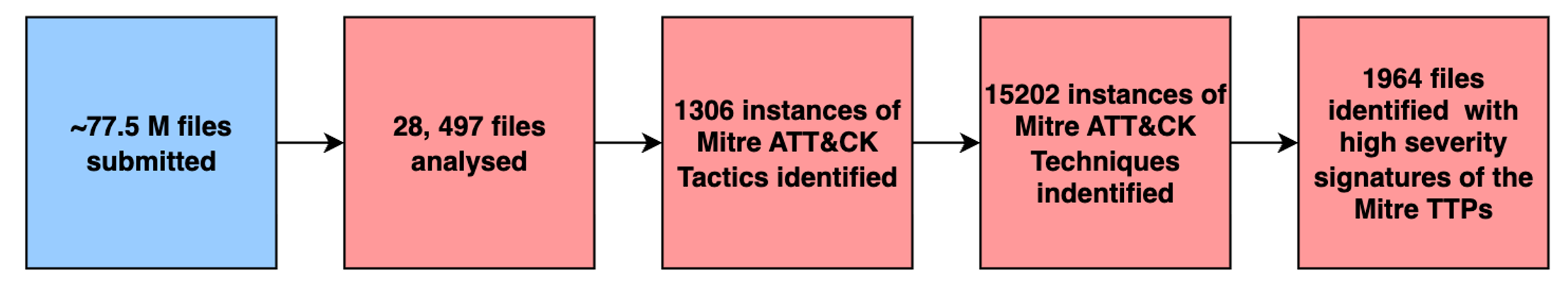
Cohesity REDLab receives malware files from a variety of sources including CISA, Google Threat Intelligence, Ransomware.live and a variety of open source repositories. TTPs are extracted by a combination of custom yara like programs and tags received from our partners like Google Threat Intelligence. In this exercise we started with about 77.5 million files. After filtering the initial set we were able to successfully extract and correlate TTPs from about 28,497 files. A total of 1306 instances of Mitre ATT&CK Tactics and 15,202 instances of Techniques were identified. In 1964 of these files, we found high severity TTP signatures signifying high-risk malicious behavior like the malware writing into another process’s memory or input capture behaviours like taking screenshots and potential exfiltration of data.
Cohesity's Resilience Against these TTPs
Top TTPs tend to change over time as attackers change their Techniques and Tactics. Customers are advised to use Cohesity Threat Scanning to scan for malware deploying the latest techniques and tactics. The Rapid Scanning feature can also be used to identify high profile malware from backups. Customers can also bring their own YARA rules for any custom requirements.
With these features, Cohesity DataHawk provides continuous malware scanning and behavioral analytics to detect process injection artifacts, keyloggers, and automated collection patterns within backup data. Our immutable snapshots via DataLock protect against T1562.001 defense evasion and T1119 automated collection attempts, preventing attackers from deleting or corrupting locked backups. Air-gapped FortKnox storage isolates critical data from network-based C2 protocols (T1071) and lateral movement attempts.
Conclusion
The backup infrastructure is not merely a recovery mechanism but an active target. It often harbors dormant malware ready to attack with new techniques. Organizations must treat backup environments with the same security rigor as production systems, implementing continuous monitoring, malware scanning, and integrity verification.
As we enter 2026, the lessons of Q4 2025 underscore the critical importance of threat-informed defense, continuous adaptation, and clean recovery capabilities validated against current threats. Cohesity REDLab will continue monitoring TTP trends and publishing actionable intelligence to help organizations maintain resilience as adversary techniques evolve.
For the latest TTP trends and advisories, please visit Cohesity REDLabs.

Ready to get started?
Start your 30-day free trial or view one of our demos.