Data management refers to the process of organizing, storing, protecting, and maintaining data throughout its lifecycle. It encompasses a wide range of activities, from data acquisition and entry to data archival and disposal. The goal of data management is to ensure that data is accurate, accessible, and secure, and that it can be used effectively for business operations and decision-making.
Data management typically involves several stages, including data planning, data acquisition, data entry, data processing, data analysis, data storage, data retrieval, and data archival. Throughout these stages, organizations must consider a range of factors, including data quality, data security, data compliance, and data accessibility. Managing data flow is crucial when dealing with data from multiple sources to maintain data integrity across platforms.
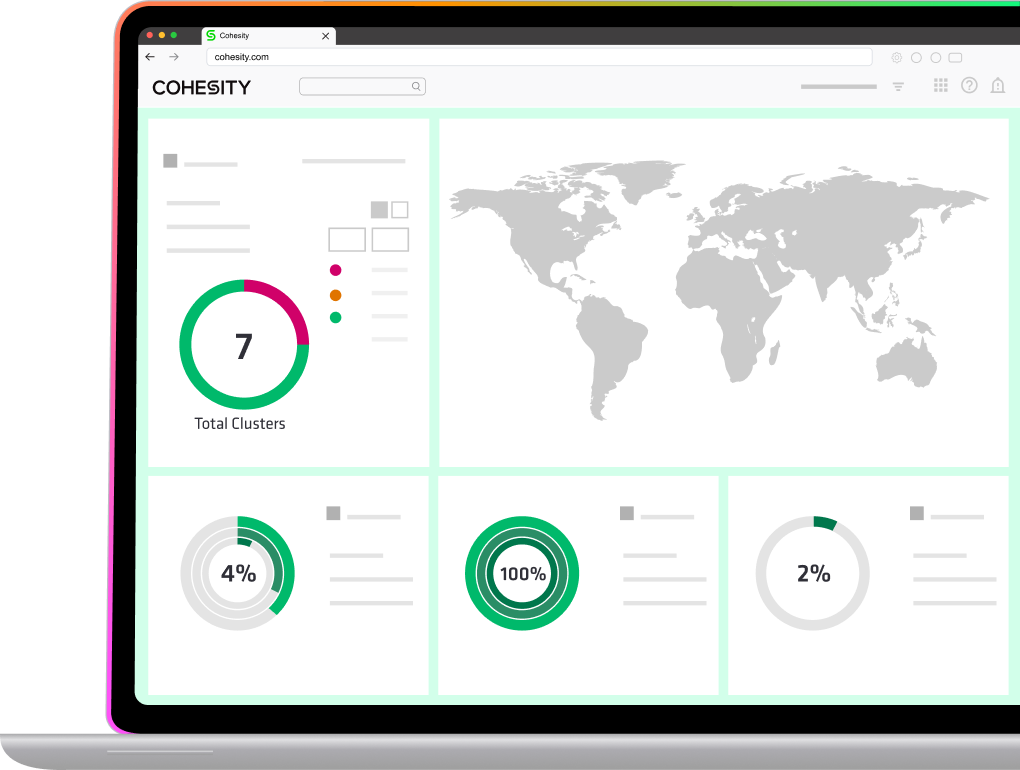
Effective data management requires IT and compliance leaders to develop and implement policies and procedures for handling data, including data governance, data security, and data privacy. It also requires businesses to leverage technology and tools to manage data more efficiently, such as data management systems, data analytics platforms, and data backup and recovery solutions. These tools tackle data management challenges like raw data transformation and integration, ensuring business intelligence systems are fueled by clean, reliable data.