GRIDTIDE - Command & Control using Google Sheets
Overview
Cohesity REDLab has released updates to its threat library in response to the active exploitation using GRIDTIDE which is a sophisticated, C-based backdoor. GRIDTIDE was at the center of one of the most far-reaching espionage campaigns encountered in recent years - confirmed across 53 organizations in 42 countries spanning Africa, Asia, and the Americas, with suspected infections in at least 20 additional nations.
Distinctive Command & Control
What makes GRIDTIDE technically distinctive is its command-and-control mechanism: rather than communicating with traditional attacker-controlled servers, the malware repurposes Google Sheets as a covert C2 channel. By routing all commands and data through legitimate Google Sheets API calls, GRIDTIDE blends its malicious traffic seamlessly into everyday cloud activity, making it exceptionally difficult to detect using standard network monitoring. This technique exploits no vulnerability in Google Sheets itself - it abuses the platform's legitimate functionality by design.

The campaign primarily targeted telecommunications providers and government organizations, with attackers deliberately deploying GRIDTIDE onto endpoints containing sensitive personally identifiable information (PII) — including national IDs, voter records, and phone numbers. This targeting pattern is consistent with surveillance-focused espionage: identifying, tracking, and covertly monitoring persons of interest.
Google coordinated a broad disruption operation: terminating all attacker-controlled Google Cloud Projects, disabling infrastructure, sinkholing malicious domains, and revoking API access – for removing persistent access to compromised environments. Victim notifications were issued to all confirmed targets. More details are available from Google at this link.
MITRE TTPs

GRIDTIDE demonstrates a focused but deliberate set of MITRE ATT&CK techniques spanning execution, persistence, privilege escalation, defense evasion, and discovery. For execution, it leverages T1064 Scripting to run malicious logic through script-based mechanisms. For persistence, it abuses T1543 Create or Modify System Process, specifically T1543.002 System Service, allowing it to establish long-term footholds by creating or modifying system services.
The same T1543.002 System Service technique is also used for privilege escalation, enabling elevated execution through service manipulation. In defense evasion, GRIDTIDE employs T1027 Obfuscated Files or Information to conceal payloads and configuration data, T1036 Masquerading to disguise malicious components as legitimate files or processes, T1064 Scripting to execute concealed logic, T1140 Deobfuscate/Decode Files or Information to unpack encoded content at runtime, T1497 Virtualization/Sandbox Evasion to detect and avoid analysis environments, and T1564 Hide Artifacts including T1564.001 Hidden Files and Directories to reduce forensic visibility.
For discovery, GRIDTIDE conducts T1016 System Network Configuration Discovery to understand network settings, T1033 System Owner/User Discovery to identify logged-in users, T1082 System Information Discovery to gather host details, T1497 Virtualization/Sandbox Evasion to detect analysis environments prior to further activity, and T1518 Software Discovery including T1518.001 Security Software Discovery to enumerate installed applications and defensive tools, allowing it to adapt behavior and improve survivability within compromised environments.
Attack Flow








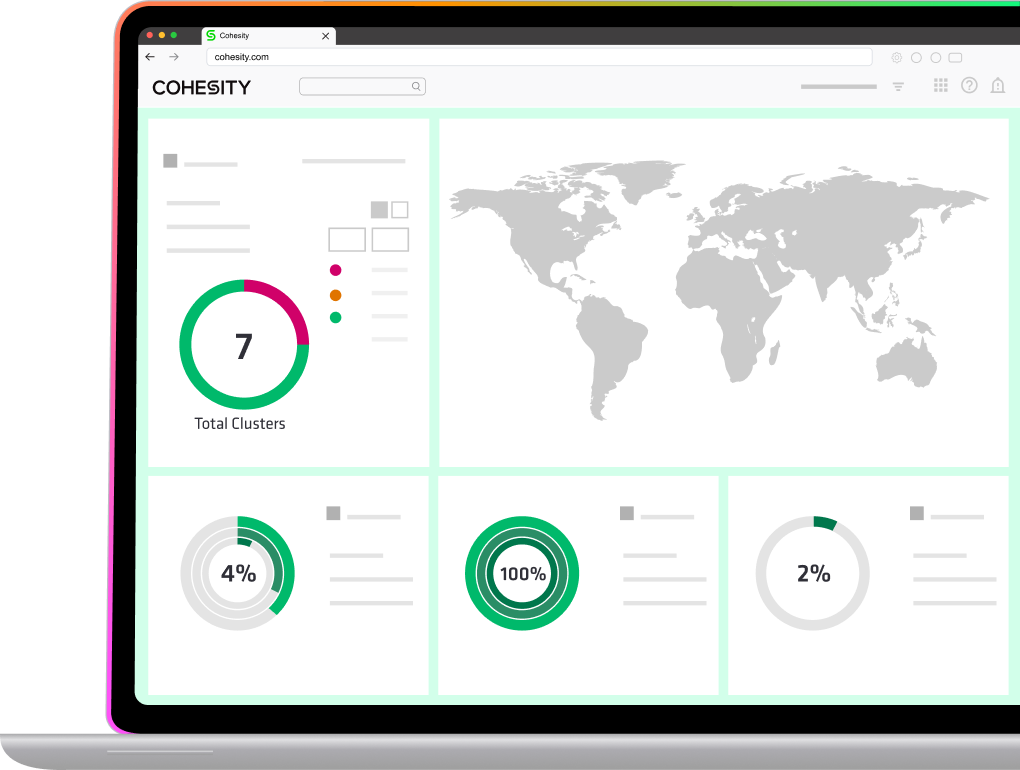
Strategies using Cohesity Solutions
GRIDTIDE is built to avoid triggering behavioural runtime detections and can remain undetected for extended periods. This is where Cohesity's rapid threat hunting and YARA rule features are valuable for analysing backup data at rest. The tool also utilises living-off-the-land binaries and erases its tracks after execution. As a result, by the time a security analyst examines the incident, any indicators have already been removed from the system. However, backup snapshots capture these indicators, and retrospectively scanning these snapshots can reveal what truly occurred.
- Rapid Threat Hunt: Use Cohesity Rapid Threat Hunts to hunt for malware using threat intelligence feeds. These feeds are updated daily with new information from intelligence sources like Google Threat Intelligence, CISA, Cohesity REDLab, Open Source and others. Users can search using default feeds or create custom feeds. More information can be found here.
- Threat Scans: Run periodic threat scans using the default threat library that is updated daily or create a custom YARA rules. Users can also use third-part integration and threat intelligence vendors. More information can be found here.
- Anti-ransomware: Users are advised to closely monitor the ML-based anti-ransomware backup anomalies in Security Center for detection of ransomware activity. More information can be found here.
- Secure Sandboxing: Cohesity’s GTI sandbox capability lets organizations safely detonate and observe suspicious or unknown files from backup data in an isolated environment to see whether they behave maliciously. It provides detailed behavioral insights like process actions, network activity, and registry changes to help security and IT teams confidently assess and remediate threats before restoring data. More info here.
- Immutable Backups: Maintain air-gapped, immutable backups to ensure rapid recovery after an attack.
- Automated Recovery: Use solutions like Cohesity’s Recovery Agent for single-click cyber recovery and clean-room restoration.
- Incident Response Playbooks: Prepare for multi-stage attacks with rehearsed response plans and stakeholder coordination.
- Pre-Recovery: Use threat detection features mentioned above before recovery to make sure that snapshots are clean.
Conclusion
GRIDTIDE's most consequential technical trait is its abuse of the Google Sheets API as a covert C2 channel, routing encrypted commands and exfiltrated data through a globally trusted domain that organizations cannot block without disrupting legitimate operations, and wrapping all payloads in AES-128-CBC encryption. Paired with a systemd persistence service, SoftEther VPN as a redundant tunnel, and exclusive use of LotL binaries for lateral movement, the toolchain is specifically engineered to leave minimal forensic footprint. Cohesity REDLab’s proactive research and validation provide organizations with the tools and insights needed to detect, respond to, and recover from GRIDTIDE and similar threats.
For the latest advisories and technical details, visit Cohesity REDLab.

Ready to get started?
Start your 30-day free trial or view one of our demos.