Understanding the importance and benefits of cyber resilience
Table of Contents
What is cyber resilience?
Cyber resilience is a set of structured guidelines designed to improve an organization’s ability to continuously deliver its intended business outcomes despite adverse cyber events and cyber risks.
This cyber resilience definition encompasses more than just security—it's about maintaining operations when successful attacks occur. These can include a breach, insider threat, ransomware attack, or other disruptive event. When your business is cyber resilient, you maintain the confidence, integrity, and availability of data while quickly recovering from cyberattacks.
Cyber resilience combines cybersecurity with Zero Trust principles, business continuity, cyber recovery, and organizational resilience strategies. It’s now a boardroom topic because threats continue to grow in number and severity. Companies are fortifying their organizations with data security and data management solutions that are both proactive and reactive to boost cyber resiliency, protect sensitive data, and maintain regulatory compliance.
Why is cyber resilience important?
Cyber resilience is important because it prevents costly downtime, protects your reputation, and ensures business continuity when cyberattacks inevitably occur.
On January 11, 2023, the unintentional deletion of files caused thousands of flights to be delayed across the United States. This is a good example of why cyber resilience is critical to enterprises’ operational stability. This sobering statistic is another—By 2031, it’s estimated that ransomware will attack every two seconds, with financial losses hitting $265B annually.
To successfully operate, your structured and unstructured data must be properly identified, protected, and accessible only to authorized individuals.
Cyber resilience helps ensure you can:
- Stay operational during an adverse event (e.g., a disaster, human error, ransomware attack, or insider threat)
- Avoid unnecessary downtime
- Protect systems from potential risks
- Maintain business continuity
- Keep data secure
- Stay in compliance with regulatory requirements
- Protect brand reputations
- Avoid paying ransom
- Detect and defend against attackers
- Recover rapidly and confidently should a ransomware attack succeed
What is a cyber resilience framework?
A robust cyber resilience framework informs a security posture that supports the continuous delivery of intended outcomes when unfavorable cyber events happen. A cyber resilience framework will include:
- Security plans, including data backup and malware detection capabilities
- Business continuity plans, including recovery time objectives and recovery point objectives (RTOs/RPOs)
- Organizational resilience plans, such as response team, communications leads, and executive sponsorship
A critical component of any cyber security resilience framework is alignment with Zero Trust security principles. By default, Zero Trust is a “never trust, always verify” security posture. Organizations following it know that devices should not be routinely and continuously trusted, even devices connected to a managed corporate network, such as the corporate LAN, and even if they were previously verified. Three principles underpin an effective Zero Trust architecture:
- User/application authentication
- Device authentication
- Trust/don’t trust philosophy
Most organizations have a critical weakness: fragmented, unprotected, unstructured data scattered across multiple clouds and locations. When you manage data with inconsistent policies and disparate tools, you create a treasure map for cybercriminals.
We recommend implementing a cyber resilience framework that unifies security across all your IT environments. The most effective frameworks give you integrated capabilities to:
- Identify —You need complete visibility across all data locations with automated threat detection that works proactively and can identify weaknesses.
- Protect — Safeguard your data with Zero Trust principles including immutable snapshots, multifactor authentication, and granular role-based access controls.
- Detect — Advanced technologies provide deep, real-time visibility so you can spot cybersecurity incidents before they spread.
- Respond — When breaches happen, you need fast, effective system restoration and streamlined incident detection.
- Recover — Get back to business quickly with instant recovery capabilities that work at enterprise scale.
- These five functions work together on a unified platform to eliminate security gaps and maintain stakeholder confidence in your organization's objectives.
What are the key components of cyber resilience?
Effective cyber security and resilience strategies combine Zero Trust principles, business continuity planning, rapid cyber recovery capabilities, and organizational resilience controls into one unified approach.
Enterprise survival depends on digital elements and infrastructure resilience, not just security. That’s because no matter how much you invest in prevention, cybercriminals continue to adapt and create more potent, intrusive malware.
A comprehensive data security and management solution should protect every source across your organization, from hardware and software products to cloud-based software products. This also includes products like IoT devices, which can introduce new vulnerabilities if left unsecured.
The 5 key steps to cyber resilience
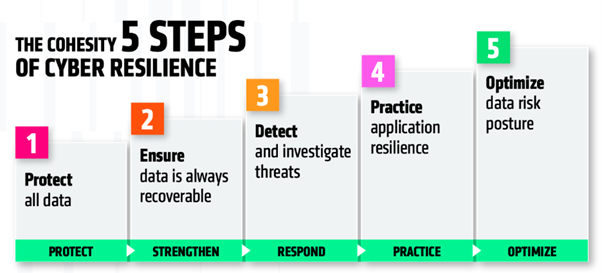
Organizations that effectively withstand and recover from cyberattacks follow a structured approach that strengthens protection, recovery, response, and risk management across their data environments.
This 5 steps to cyber resilience framework focuses on five key actions to reduce risk and ensure rapid recovery:
- Protect all data – Secure data across all environments to reduce exposure.
- Ensure recoverability – Safeguard backups so data can always be restored after an attack.
- Detect and investigate threats – Continuously scan for and analyze potential threats.
- Practice resilience – Regularly test and rehearse recovery processes to ensure readiness.
- Optimize risk posture – Continuously assess and reduce data risk through visibility and classification.
Together, these steps provide a practical foundation for building strong cyber resilience. Learn more about Cohesity’s 5 steps to cyber resilience.
What is cyber resilience vs cyber security?
Cybersecurity focuses on preventing attacks, while resilience in cyber security ensures you continue operations and recover quickly when prevention fails.
With a robust cyber resilience strategy, you can identify, protect, and detect ransomware and other evolving threats. More importantly, you can rapidly respond and recover without a significant impact on your business operations, maintaining customer trust in your ability to safeguard their sensitive information.
Cyber resilience metrics
Cyber resilience metrics measure how effectively your organization can prevent, respond to, and recover from successful cyberattacks.
Key metrics include:
- Frequency of backups, vulnerability scans, and security patching.
- Strength of role-based access controls and authorization levels.
- Recovery time objective (RTO) for returning systems to normal operations.
- Recovery point objective (RPO) for acceptable data loss before restoration.
- Number of integrated security solutions working across your infrastructure.
- Results from a cybersecurity risk assessment or comprehensive risk assessment.
TechTarget offers a cyber resilience assessment that can answer your questions, like what to measure when determining the strength of your organization’s cyber resilience strategy.
Cohesity and cyber resilience
You can strengthen cyber resilience with Cohesity’s unified approach to data protection. When you rely on siloed point products for backup, disaster recovery, ransomware recovery, and file services, you inadvertently widen your attack surface and make it harder to defend against threats.
The Cohesity data cloud platform consolidates vulnerable infrastructure silos on a single, scalable, secure platform. It better protects your data while improving security posture with security controls and company-wide cybersecurity awareness program.
With the Cohesity platform, you have a simpler way to:
- Identify — Cohesity delivers global visibility across environments and cyber vulnerability scanning to proactively detect threats and potential vulnerabilities.
- Protect — The Cohesity data security and management platform effectively safeguards data and reduces the risk of unauthorized access with immutable backup snapshots, immutable file system, encryption inflight and at rest, WORM (write once, read many), multifactor authentication, granular role-based access, and no service back door. Cohesity also features modern data isolation with cyber vaulting.
- Detect — Cohesity’s proactive approach to seeing and detecting attacks to stop encroachment includes machine learning (ML)-based anomaly detection, deep visibility of affected objects and sources, and real-time notifications, alerts, and security updates.
- Respond — If systems are breached, Cohesity provides integration to security operations to alert security teams and leverage an established incident response process. We also have a global CERT team to help you assess the health of backup data and aid in decisions about recovery points. This includes built-in auditing and reporting as well as granular Active Directory comparison capabilities.
- Recover — To get back to business quickly after an adverse event, our platform features instant recovery at scale for virtual machines (VMs) and non-disruptive instant large database recovery. You can recover to any location and any point in time, and use our recommended clean snapshots to ensure you're restoring from uncompromised data.
When you need to minimize both RTO and RPOs in today’s always-on business environment, we unify your entire data protection infrastructure—target storage, backup, replication, disaster recovery, and cloud tiering—on one platform for faster results.
Beyond fast, flexible backup data and system protection, preventing unauthorized access, stopping encroachment early, and supporting rapid recovery at scale, we boost your cyber resilience through platform extensibility. The Cohesity platform is tightly integrated with leading security orchestration, automation and response (SOAR) and security information event management (SIEM) solutions to accelerate discovery, investigation, and remediation of ransomware attacks. You also get an SDK and customizable management APIs for the flexibility to address your unique business requirements.
Cyber Resilience FAQ
Cyber threats don't wait for you to be ready. We've answered the most common questions organizations ask when building resilience strategies that work.
How do you build cyber resilience?
You build cyber resilience by unifying data protection on a single, secure platform instead of relying on fragmented point solutions that create gaps.
We recommend starting with Zero Trust principles—never trust, always verify. Consolidate your backup, recovery, and security tools into one platform that can identify threats across all environments, protect data with immutable snapshots, detect anomalies through machine learning, respond with automated incident workflows, and recover your systems instantly at scale.
What are the challenges of cyber resilience?
Most organizations struggle with siloed systems, sophisticated attackers, and the complexity of protecting data across hybrid cloud environments.
When your backup, security, and recovery tools don't talk to each other, you're essentially handing cybercriminals a roadmap of vulnerabilities. Add the challenge of maintaining consistent security policies across on-premises and multiple cloud environments, and you can see why many teams feel overwhelmed by the complexity.
What does effective cyber resilience look like?
Effective cyber resilience means maintaining operations during attacks and bouncing back quickly without paying ransoms or losing weeks of productivity.
You'll know you're resilient when threats are detected in real-time, compromised systems are isolated instantly, and clean data is restored within minutes, not days. Your team has complete visibility across all environments and the confidence from knowing your recovery processes work when you need them most.
You May Also Like
Get started today
Enjoyed your demo? Experience the power of cloud backup and recovery—free for 30 days.